Parimatch Bookmaker and Casino in Pakistan
Parimatch History
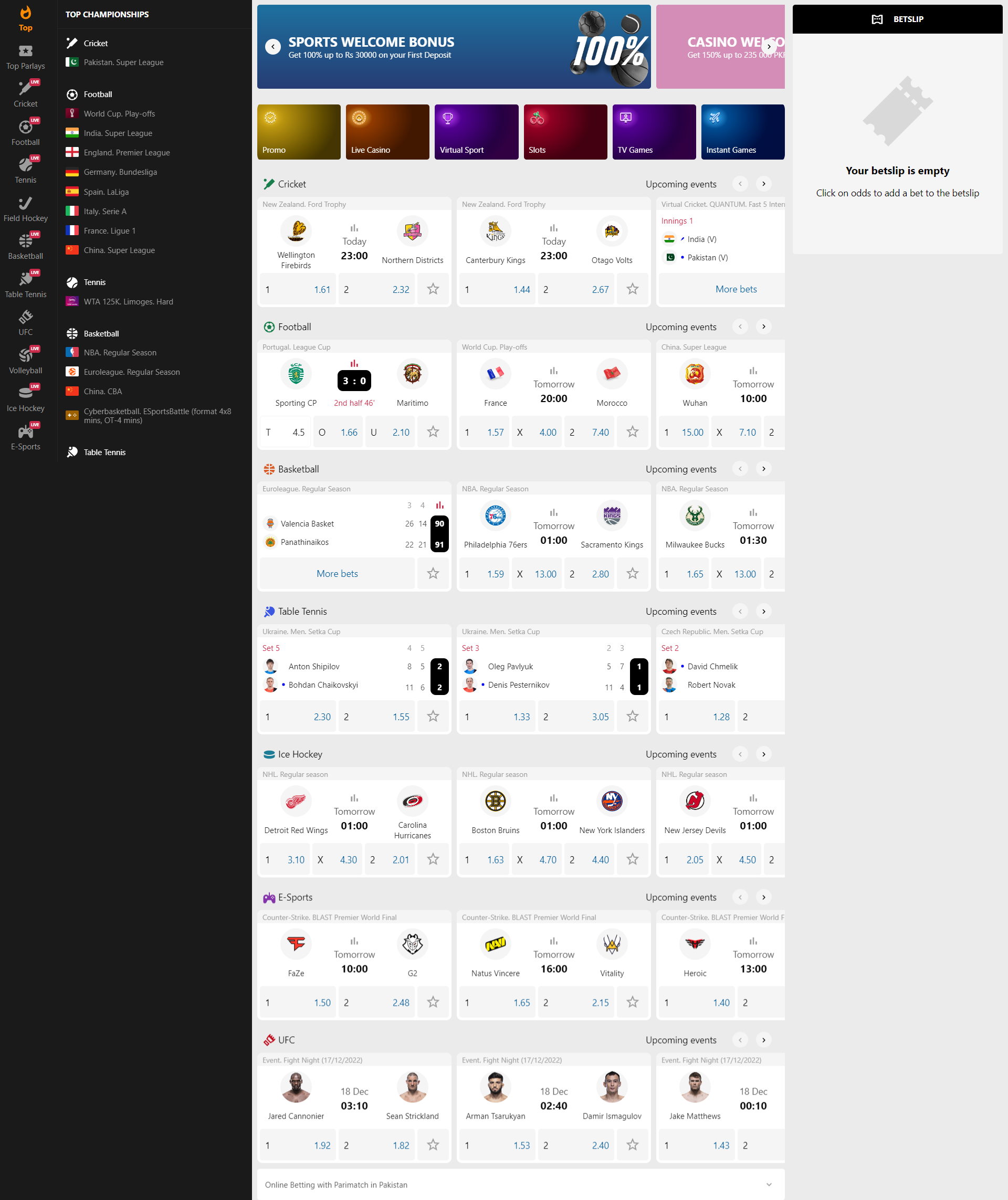
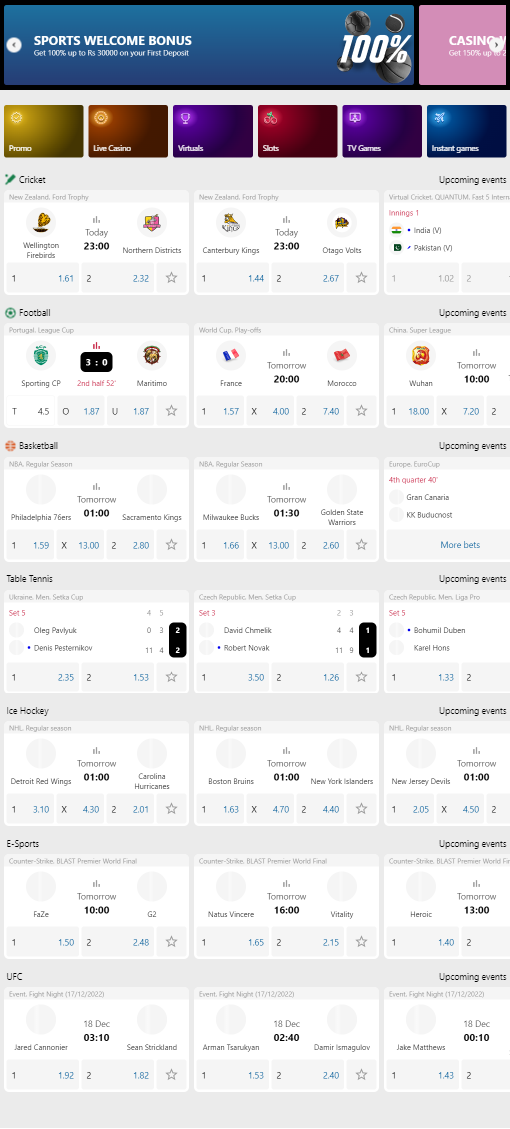
Betting on sports is not the only service that Parimatch Casino can offer its customers. The offshore bookmaker provides users with access to a wide selection of slot machines from providers from all over the world. Offline slots, real dealers and its own poker room allow “Parimatch” to remain one of the leaders in the gambling industry.
“Parimatch” has gained widespread popularity thanks to sponsorship contracts and cooperation with the stars of the UFC scene. In 2019, Conor McGregor and Mike Tyson became ambassadors of the brand, which significantly increased the popularity of the online casino. In addition to advertising, the company’s success is due to its wide functionality and reliable protection of customer data – in addition to encryption systems, employees constantly remind bettors about security measures for the account.
Registration at Parimatch Casino
To create an account on the official website of Parimatch, it is enough to click on the corresponding button at the top of the screen. To begin, the client needs to specify a phone number, preferred currency and password to enter the account. It is noteworthy that only adult players are allowed to use the services of the online casino. Next, a confirmation SMS code will be sent to your phone number. It can be omitted and postpone the procedure for later, the account, in any case, has already been created. We recommend that you go straight to your personal cabinet and fill out a questionnaire about yourself. In addition to the standard information about your place of residence, full name and date of birth, Parimatch will offer you to choose and answer a secret question to facilitate password recovery if necessary.
In the personal cabinet, information about bets and financial transactions is available. You can also change your details and view deposit/cashout methods. “Promotions and bonuses” contains offers available to the client.
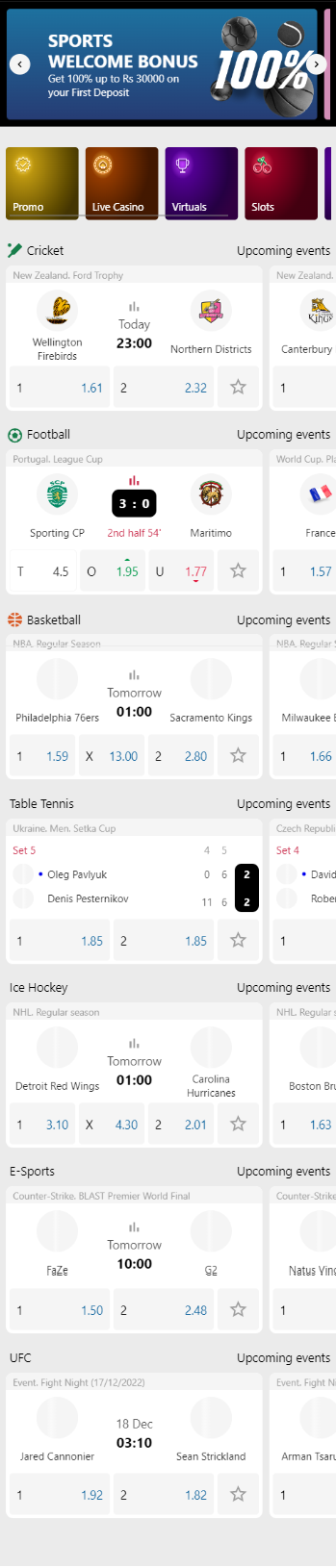
Parimatch Mobile App
The online casino app is available on Android and iOS devices. It is better than the mobile version for several reasons – the program automatically connects to a working mirror, consumes less traffic and is more convenient to use. You can download the software from the official Parimatch website, where the installation files and a link to the App Store are located. After installing the Parimatch casino mobile application, the user will be offered to register or authorize in an already created account. The procedure can be postponed for later by clicking on the cross at the top of the screen. In this case, the client will get to the title page, identical to the mobile version of the BC.
Try out slot machines without authorization will not work, as the casino immediately redirects the user to the login window. A few words about performance – the mobile application works promptly even on weak devices, the pages load quickly. Slots filtering is adapted to smartphones, entertainment is divided by providers and types of games.
Slot machines
Gambling entertainment is divided among themselves corresponding sections. For convenience, the pages have a search by keywords – a convenient feature if the user knows the name of the slot machine. Thus, the online casino Parimatch has four sections dedicated to gambling:
- Virtual Sports;
- Casino;
- Live Casino;
- Sports Poker.
In addition to these sections, the company is known for its status as a bookmaker. “Parimatch” gives a line on sports and computer disciplines, but the main development is observed in the cybersports direction. Do not confuse this with virtual sports, the outcome in which depends solely on the algorithms of online casinos.
Slots and Live Casino
Slots on the Parimatch website are presented by more than 25 providers, among which there are some exclusive ones. Slots are filtered by category – some of the entertainment indicates the number of lines and possible jackpot. Additionally, there is information on bonuses and current tournaments.
If the user prefers to play with live dealers, he should go to the “Live Casino” section. Customers are offered classic card disciplines, roulette and other games like Wheel of Fortune. Similar to slots, the page has information regarding bonuses. On top of this is added the “Rules”, which outlines the basic data about the Live Casino and the conditions of spending time in it.
Poker and free games
Parimatch has a separate site for sports poker. To play, you need to register and install the client on a PC or mobile device based on Android and iOS. In addition to download links, the portal has information about the rules of the game in the card discipline and tips that a beginner will need. There are also special promotions dedicated to poker, but according to the news, they have not been updated since 2019.
You can play at Parimatch Casino for free, but to do so you need to participate in one of the company’s promotions. The welcome bonus, for example, gives new customers up to 300 freespins for a particular slot machine. With special luck, the free spins can be wagered and withdrawn to the wallet from which the first deposit was made earlier.
Bonus offers from Parimatch casino
To maintain interest in the game, clubs offer different promotions and bonuses. Among the most popular in Parimatch are such:
- Welcome bonus when playing slot machines – given to new users on their first deposit.
- Cashback 10% when playing on weekends in the live mode – to get it, you need to write to tech support on Monday. Within three days the reward will be credited.
- Cashback 20% for weekend play at Betgames – real money lost in betting is taken into account.
- Jackpot – can be held on soccer, dota, hockey events. You have to place 15 bets and if you win 10 of them, you get the jackpot.
Only registered users can get Pari-match casino bonuses, they are not available at demo game.
Conclusion
Parimatch casino works honestly, faithfully pays out winnings and earned bonuses. The institution is constantly improving and updating its functionality. Thanks to this, the demand for the services of the playground is constantly growing and not only among Pakistanis, but also among citizens of the Eurasian continent.
